Vulnerable Code [Comic]
This comic depicts a conversation regarding vulnerable code. Can the characters agree as to whether this is a good or bad thing?
Join the DZone community and get the full member experience.
Join For Free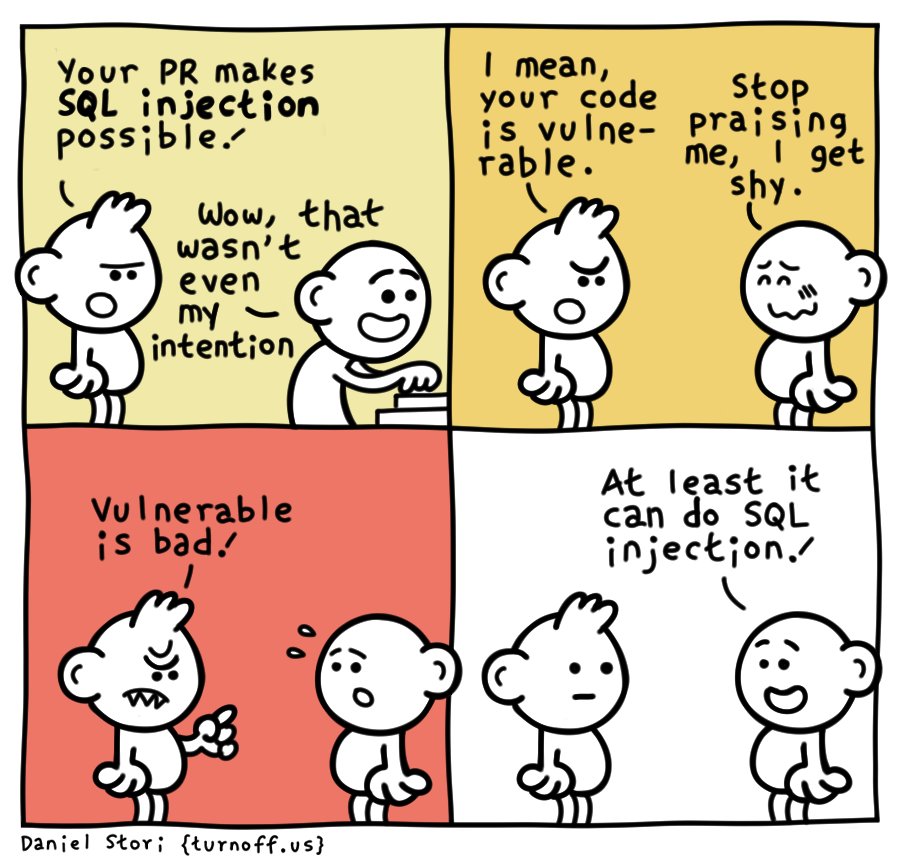
Alternative Text: This comic depicts an interaction between two characters and is split into four panes.
In the upper left pane, Character 1 enters the scene with a slightly agitated expression and comments to Character 2, "Your PR makes SQL injection possible!" Character 2, who is typing away at their computer, responds happily, "Wow, that wasn't even my intention," as if Character 1 has paid them a compliment.
In the upper right pane, Character 1, now with an increasingly agitated expression, says, "I mean, your code is vulnerable." Character 2, now standing and facing Character 1, is almost proudly embarrassed at what they take as positive feedback and replies, "Stop praising me, I get shy."
In the lower-left pane, Character 1, now shown with sharp teeth and a scowl, points a finger at Character 2 and shouts clearly, "Vulnerable is bad!" Character 2 seems shocked at this statement, standing with their mouth and eyes wide open.
In the lower right and final pane of the comic, Character 2, smiling once again, replies with the comment, "At least it can do SQL injection!" Character 1 stares back at Character 2 with a blank expression.
Opinions expressed by DZone contributors are their own.

Comments